OSINT Automation
5 Days online
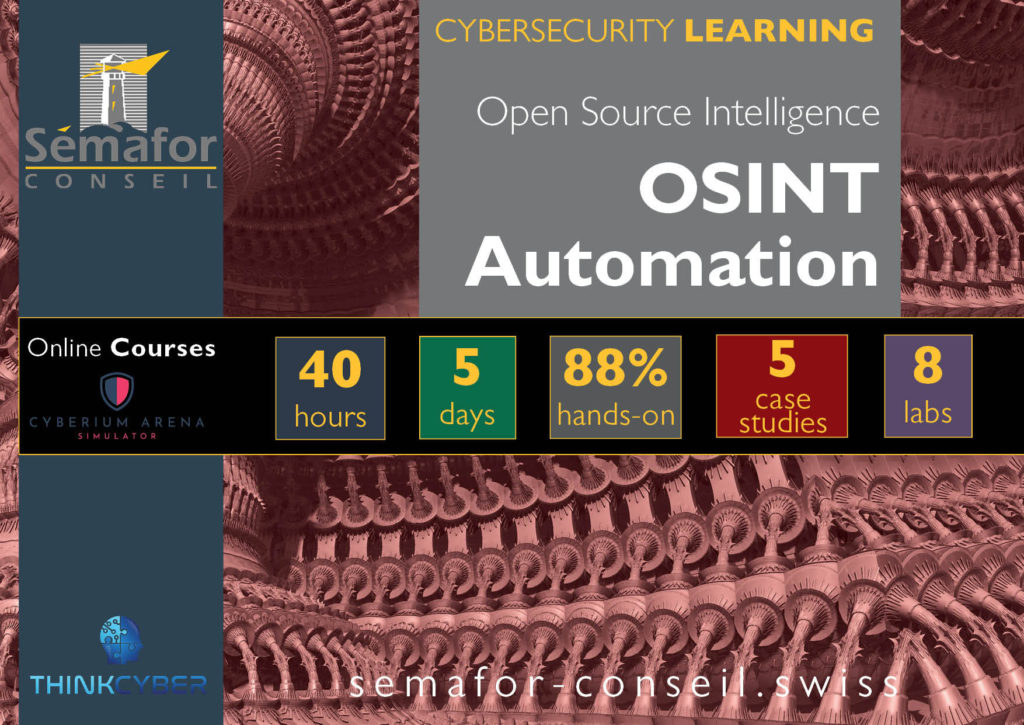
Open-source intelligence (OSINT) Automation covers the techniques and procedures used to retrieve targeted information from open-source networks containing huge amounts of data using automatic tools to achieve maximum results.
This course teaches participants how to collect and analyse information using different tools and creating automation. Participants will be further exposed to collecting information from the Darknet, social networks, and other sources.
The course helps prepare for the certification exams GOSI (SANS) and C|OSINT (Mcafee).
This course is essential for:
This course targets mostly law-enforcement wanting to master the art of finding data around the internet.
- Threat intelligence analysts
- Cybersecurity professionals
- Law enforcement personnel
- Intelligence officers
- Private/public Investigators
- Forensics investigators
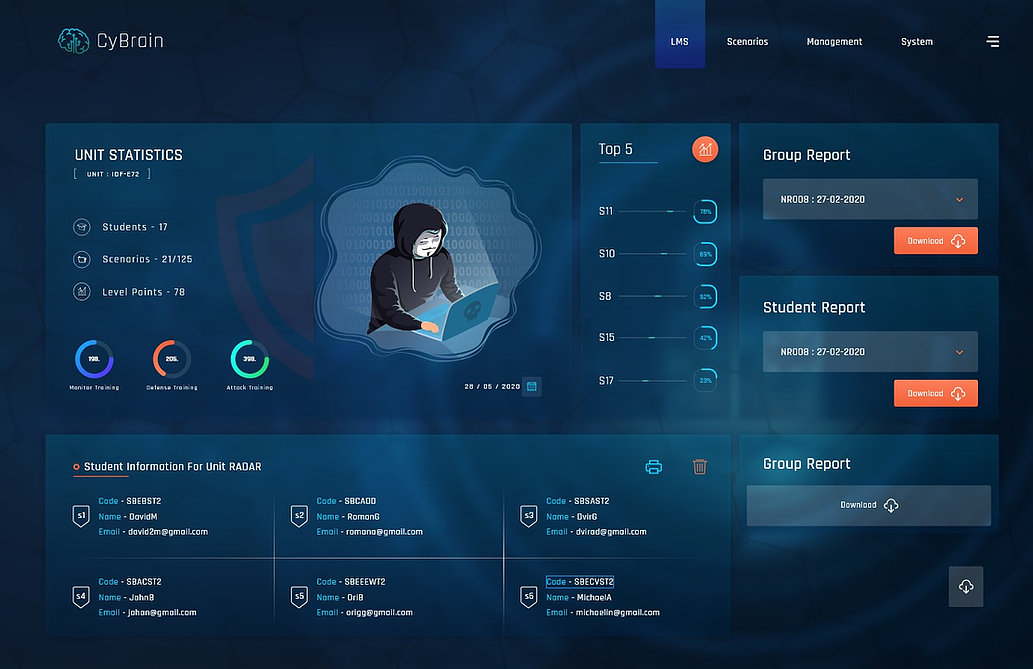
Cyberium Arena

Real Cases Studies
Remain informed about the schedule:
More about:
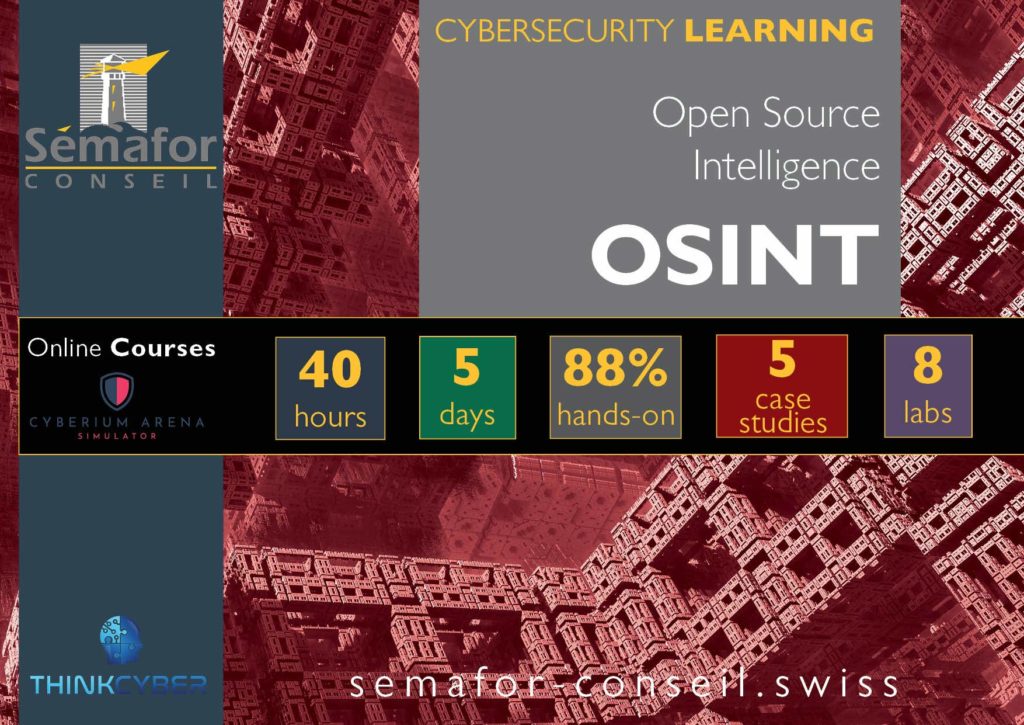
Open Source Intelligence basic course is the first step to learn about searching targeted informations among the immense data sources available for public through the Web, Darkweb, Social Networks and others sources.
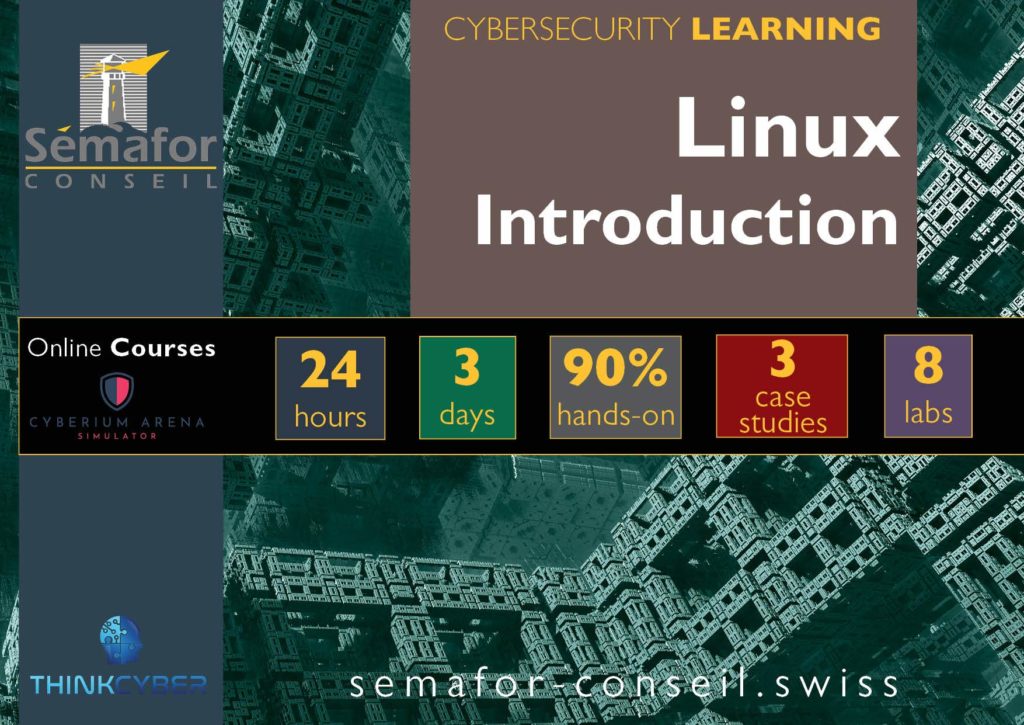
Linux system is essential for OSINT and specifically OSINT Automation. Learn the basement of Linux with this introduction course. Linux can be installed as a sub-system of Windows without affecting your computeur.