Cryptography
5 Days online

Cryptography is an indispensable tool for protecting data in computer systems. With this course, you will learn the inner workings of cryptographic systems and how to use them correctly in real-world appliations.
From ancient examples of secret messages and the spies that cracked them to modern cryptographic applications, you will have the opportunity to explore the foundations of data security.
This course is essential for:
- Cybersecurity beginners
- Anyone intersted in cryptography
- Anyone curious about how how data is encrypted to be secured
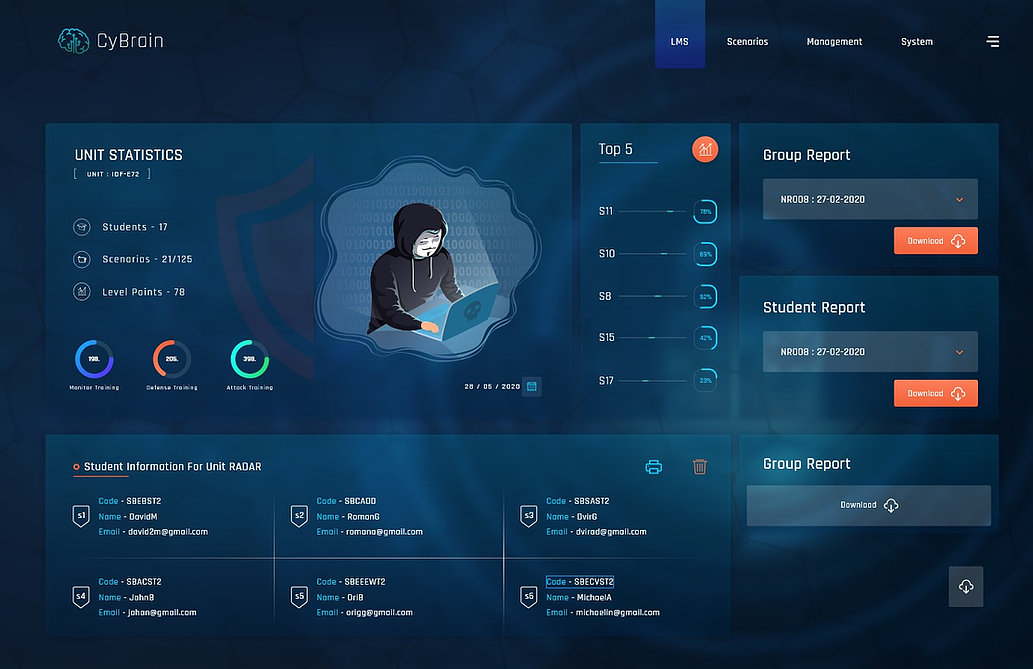
Cyberium Arena

Real Cases Studies
Remain informed about the schedule:
More about:
The Introduction to cybersecurity course is for managers, business leaders or anyone who wants to discover the cyber world and security threats.
The Linux Introduction course is for people who want to begin with the Linux System, the most adapted for cybersecurity operations and development. Linux can be installed as a sub-system of Windows without affecting it.