Network Security
5 Days online
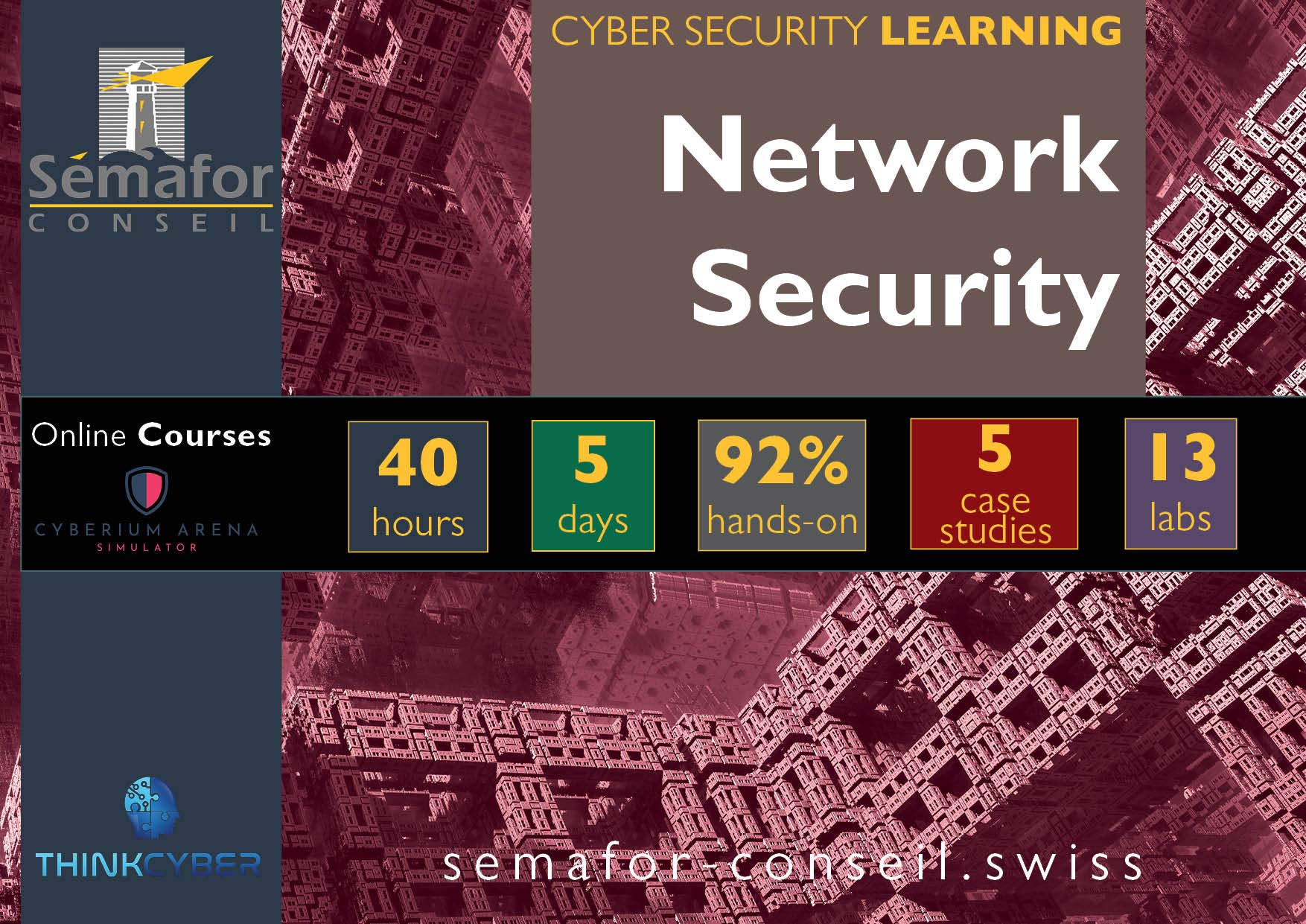
Network security is a broad term that covers multiple technologies, devices, and processes. Nowadays, every organization, regardless of size, industry, or infrastructure, requires a network security expert in place to protect it from the ever-growing landscape of cyber threats.
During this course, you will discover security vulnerabilities across the entire network using network hacking techniques and vulnerability scanning. You will understand the various types of firewalls available and master both Windows and Linux servers’ hardening.
The course helps prepare for the certification exams CySA+ (CompTIA), Security+ (CompTIA), GISP (SANS), and GISF (SANS).
This course is essential for:
- Computer or network specialists who want to turn their knowledge into security perspectives
- Network operatives
- Programmers & Developers
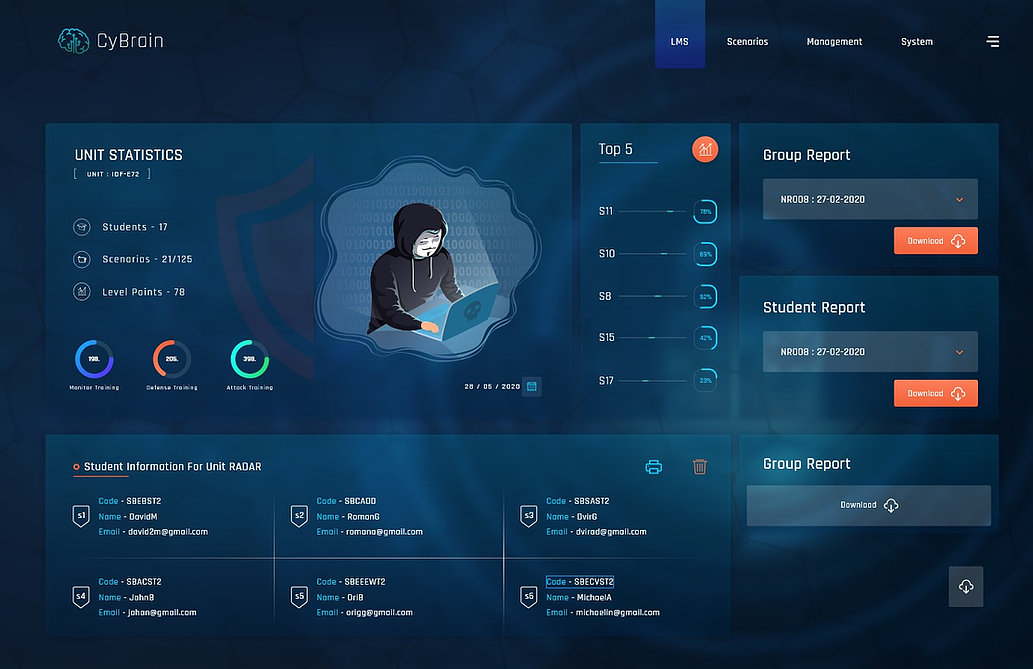
Cyberium Arena

Real Cases Studies
Remain informed about the training schedule:
More about:
The Penetration Testing course is the logical next step in acquiring network defence skills.
The SOC Analyst course lays the groundwork for implementing an updated Security Operations Centre in the face of the cyber threats we face today.