Cybersecurity Comic Strips
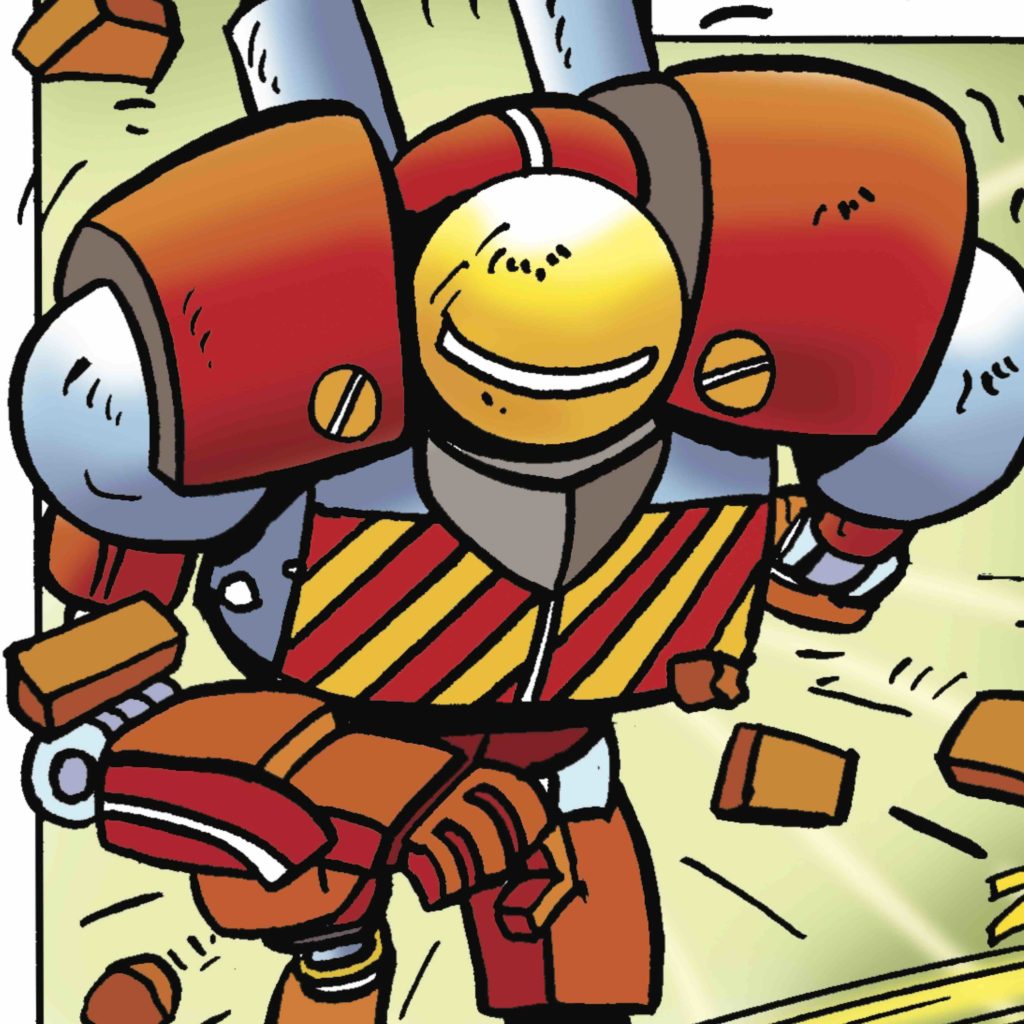
Throughout its 25 panels, the cybersecurity comic strip deals with all the major themes in the risks of digital aggression, and this on 4 main fields of application:
General risks
Whether at work or at home, in our professional or social relationships, we must all be aware of the powerful negative impact of a digital aggression of which we could be victims.
Persistent threats
Understand the risks of cyber warfare conveyed by the Internet and the role of each to prevent its spread.
Our bank account has changed
The security bases to be set up within the company and the behaviour to be adopted by all employees.
Smartphones have ears
The essential safety rules for mobile phones
Cyberattack, it only happens to others

Learn useful precautions to avoid traps.
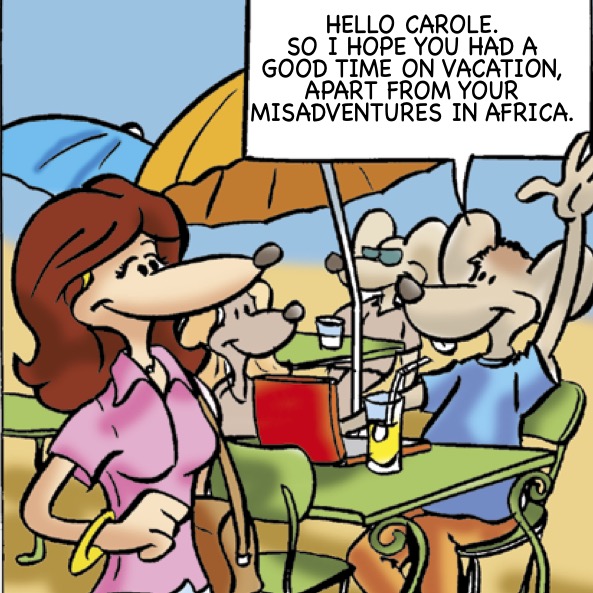
Back from vacation
While passwords are the key to all systems, computers, applications, etc. it is so difficult to manage them effectively!
Meeting the information
Information is all that is useful to the business lines and to all the activities of the organization enabling them to achieve their objectives: from data managed in applications to electronic messaging via office automation, intranet, website or configuration settings, and more.
Tracking down pirates (Swiss copyright)
Discover your best ally... or your worst enemy!

A person’s private sphere is a precious asset that enjoys special protection, including in the world of work and health.
Homo Domoticus or the Internet of Things
A car, toy, medical device, home appliance or any other object that may contain an information system and that connects to a wider network via WIFI, bluetooth, or through a smartphone or other system that drives it.
Management and HR
The cybersecurity framework is governed by laws, policies, rules and standards and our organizations must comply with them. It is the responsibility of Management and Human Resources to ensure this.
Private access

Data access management inside the company and security policy.
The boss's nightmare (RGPD)
Human Resources security. Private data protection (DPGR).
1 click and Hop! (security policy)
Emails security rules, what the company has to do and what the employees must apply.
The sales room
Among cybercrimes, the information hacking can have serious conscequences.
Risk analysis
A general methodology of cyber risks.
The little devils are hiding in the details
Apps security
A good plan

Business Continuity Management
All the light on confidential information!
Security measures to be organized within the company and the precautions that all employees must observe to avoid a leak of information.
Telecommuting, travel and business trips
Digital risk has no boundaries, so in private life we must apply the same rules as in professional life, plus some that are specific to it.
Heard in the bus

The instructions to be followed by all employees and the organisational measures essential within the company.
Webconference
About Web conferences and critical security aspects.
All at home (free)

Securing computer tools both in telework and at home school.
Private Life
Cyberrisk has no boundaries, so in private life we must apply the same rules as in professional life, plus some that are specific to it.
I protect my information even at home
Broken heart
Vulnerability of your computer and personal information.
Cell phone: it knows everything about you!

Security of mobile phone, communications, common applications, games, social networks, e-commerce, etc.
We are between us and yet
About publications confidentiality on social networks.
Les auteurs
Jacqueline Reigner

Dr. Sciences of the University of Lausanne, founder of Sémafor Conseil SA and honorary president of the Swiss Association for Information Security – Clusis, Jacqueline Reigner imagined an original training program: The Cybersecurity Comic Strips
Gianfranco Brunetti

Gianfranco Brunetti, artist, graphic designer, illustrator and creator of Comics strips.
Designer with Jacqueline Reigner and graphic designer of La BD de la Cybersecurity.
Gianfranco Brunetti is well known for his creations and especially for “La Ferme à Bolomey”.
Website : http://illustration-brunetti.ch
Shirudo

Discover Shirudo, Serious Game, an immersive short-form educational tool to train your staff in the right uses of cybersecurity.
